Reverse Engineering AI Answers: What I Learned Building a Custom AEO Pipeline
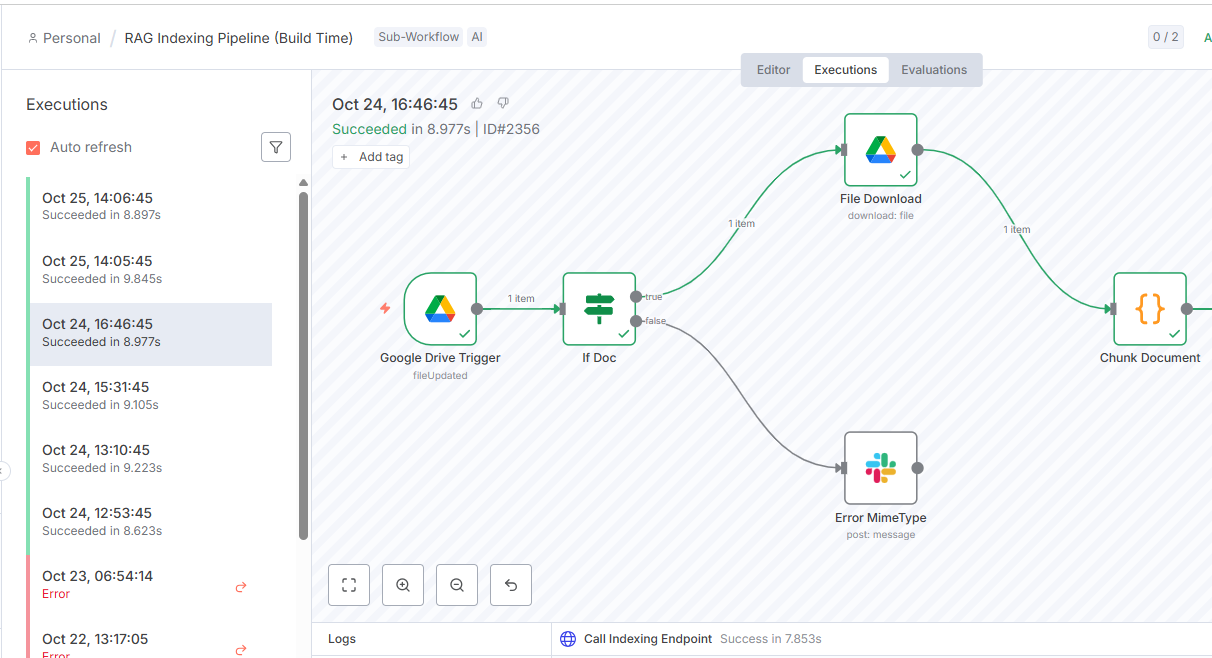
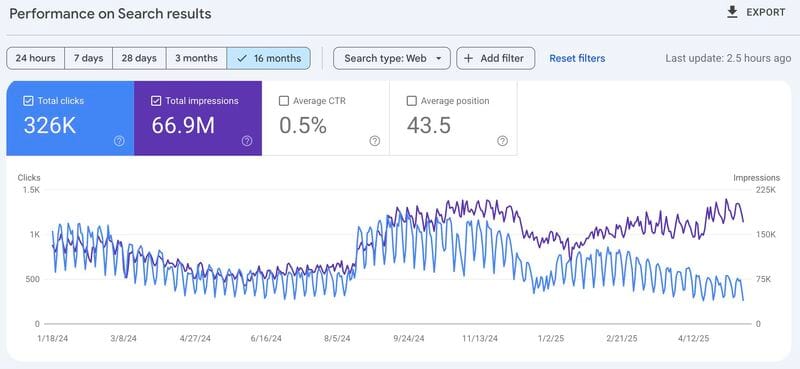
I built a custom AEO pipeline and learned that retrievers, not generators, break RAG systems. Here is what Context Rot costs you and how to stop it.
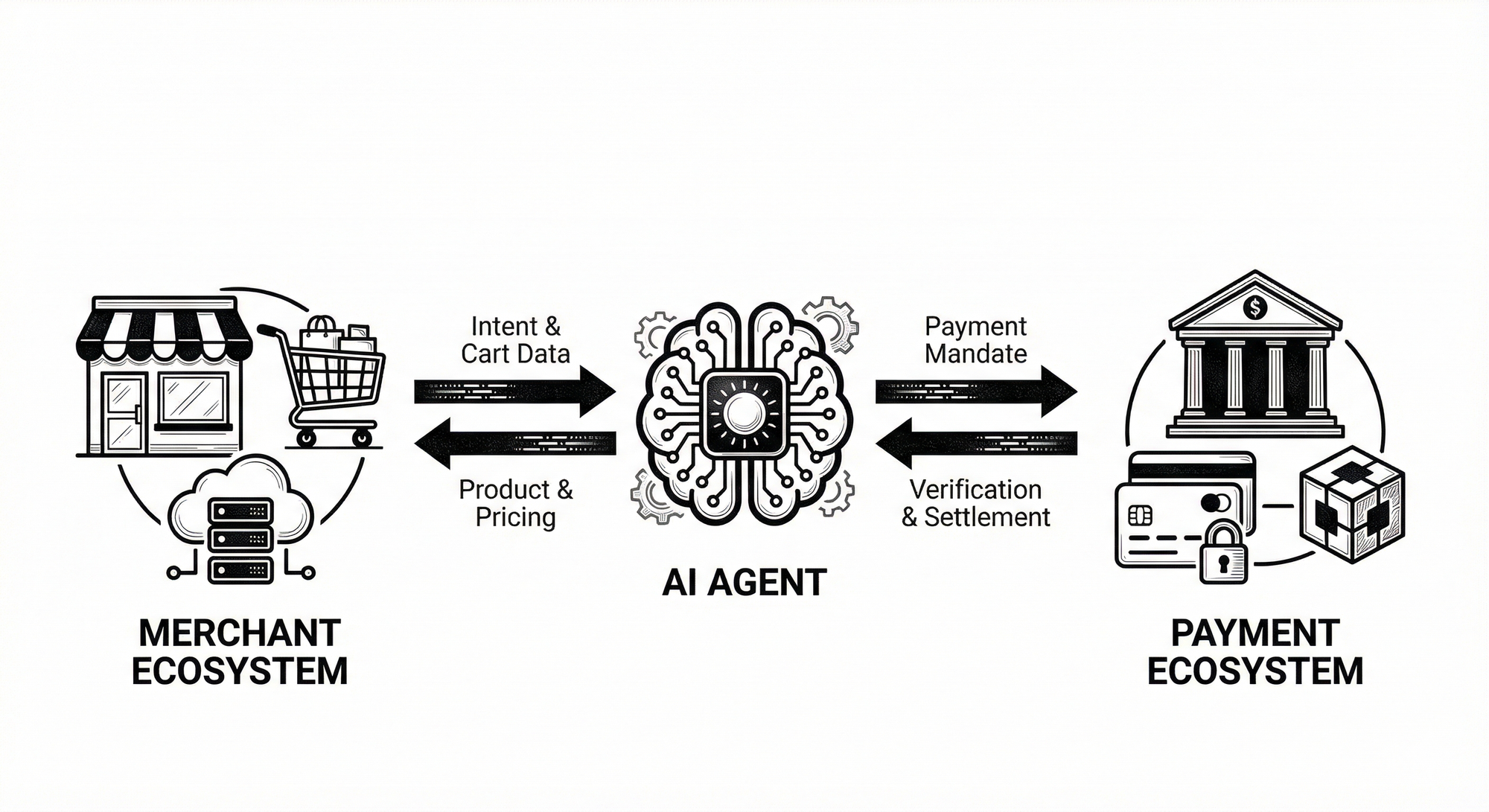
How to Enable AI Agents to Make Purchases: Complete GMC Integration Guide
Build secure agent-driven purchases with GMC V1, ES256 signatures, HMAC binding, and immutable consent proofs. Production code, compliance mapping, and deployment checklist included.
Solving AI Agent Payment Authentication: A Technical Guide to AP2 Mandates
Are your agent payments vulnerable to the Symmetric Fallacy? Learn how to pivot to Asymmetric keys (ES256), build a dumb Signer primitive, and implement a robust Policy Engine (PDP) for secure Agentic Commerce.
What I Ordered vs. Got: Implementing Consumer Protection for Agentic Commerce in Nigeria & South Africa
"What I Ordered vs. Got" is moving from a viral meme to a systemic risk for AI agent commerce. This guide shows senior leaders how to close the trust gap using AP2 and Intent Mandates, mapping technical traceability directly to NDPA and POPIA compliance.
Designing Fair Personalization: Ethical Upsell Strategies for Third‑World Consumers
Can purely algorithmic upsells be fair? Explore technical safety strategies (AP2/A2A) that build long-term trust and protect consumers in low-bandwidth markets.
AI & African Creativity: Who Keeps the Copyright?
Tools do not inherit culture; people do. If we design models, contracts, and markets that ask creators to teach the machine and then deny them the receipts - the rights, the pay, the credit - we will have built a clever silence.