Solving AI Agent Payment Authentication: A Technical Guide to AP2 Mandates
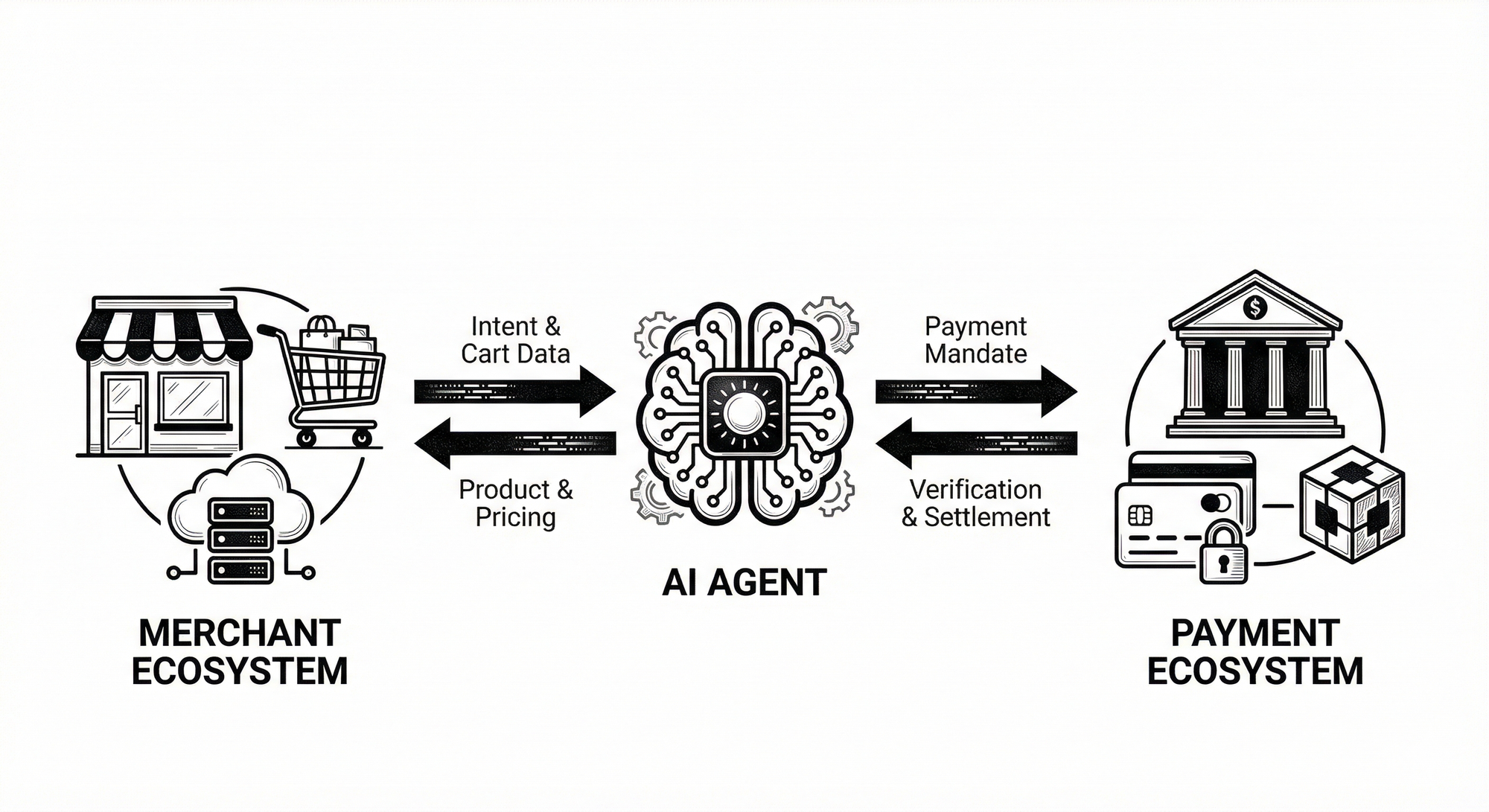
Agent Payments Protocol (AP2) mandates now underpin agent-driven payments in both experiments and early production. Public specs describe mandates as cryptographically signed proof of intent and rules for execution. The project documentation emphasizes how mandates carry the original shopper intent which agents present to merchants. See AP2 Core Concepts. This introduction explains why current practices create a Validation Chasm and why security must separate cryptographic proof from business authorization. Think of cryptographic signatures as a verified (validated) document. Signatures prove content integrity but do not automatically prove authority to spend.
Two failure modes cause most breaches in agent payments. First developers often treat symmetric HMACs (Hash-based Message Authentication Codes) as both proof and permission which enables forgery when verifying parties also hold keys. Community posts and protocol critiques document this Symmetric Fallacy and its operational liability. Second some cart mandates lack binding to parent intents which lets forged lineage pass simple signature checks. Legal and engineering commentary has raised alarms about orphaned credential attacks and their downstream settlement risk.
This guide prescribes an Asymmetric Pivot to ECDSA (Elliptic Curve Digital Signature Algorithm) signing so signing keys differ from verification keys. That separation forces checks that go beyond signature validity. It then elevates the validation logic into an independent Mandate Policy Engine that inspects business rules and chained intents. Keep the signer minimal and deterministic. Let policy engines decide whether a signed claim can convert into spending authority.
We will define a Hierarchical Hash Binding pattern where every Cart must carry a nested JSON Web Token-intent (JWT_intent) digest signed by the root intent. That creates a cryptographic chain of custody which tightly links child carts to the original authorization. Imagine a signed family tree where each child carries a fingerprint of its parent. Nodes may restrict budgets and merchants but cannot expand permissions set by their parent.
This article also provides concrete code changes and defensive schema edits that you can vet during a security review. You will see how to add parent_intent_id and intent_digest to anap2.py model. You will get a signer.py that produces ES256 tokens and verifies nested digests. It also includes a monotonicity decorator that asserts cart.final_amount stays within intent.max_budget.
We will evaluate failure modes and propose low latency revocation using Bitstring Status Lists to reject compromised JTIs (JWT IDs) without heavy state. The guide contrasts short lived tokens with structural revocation gaps and recommends a hybrid approach.
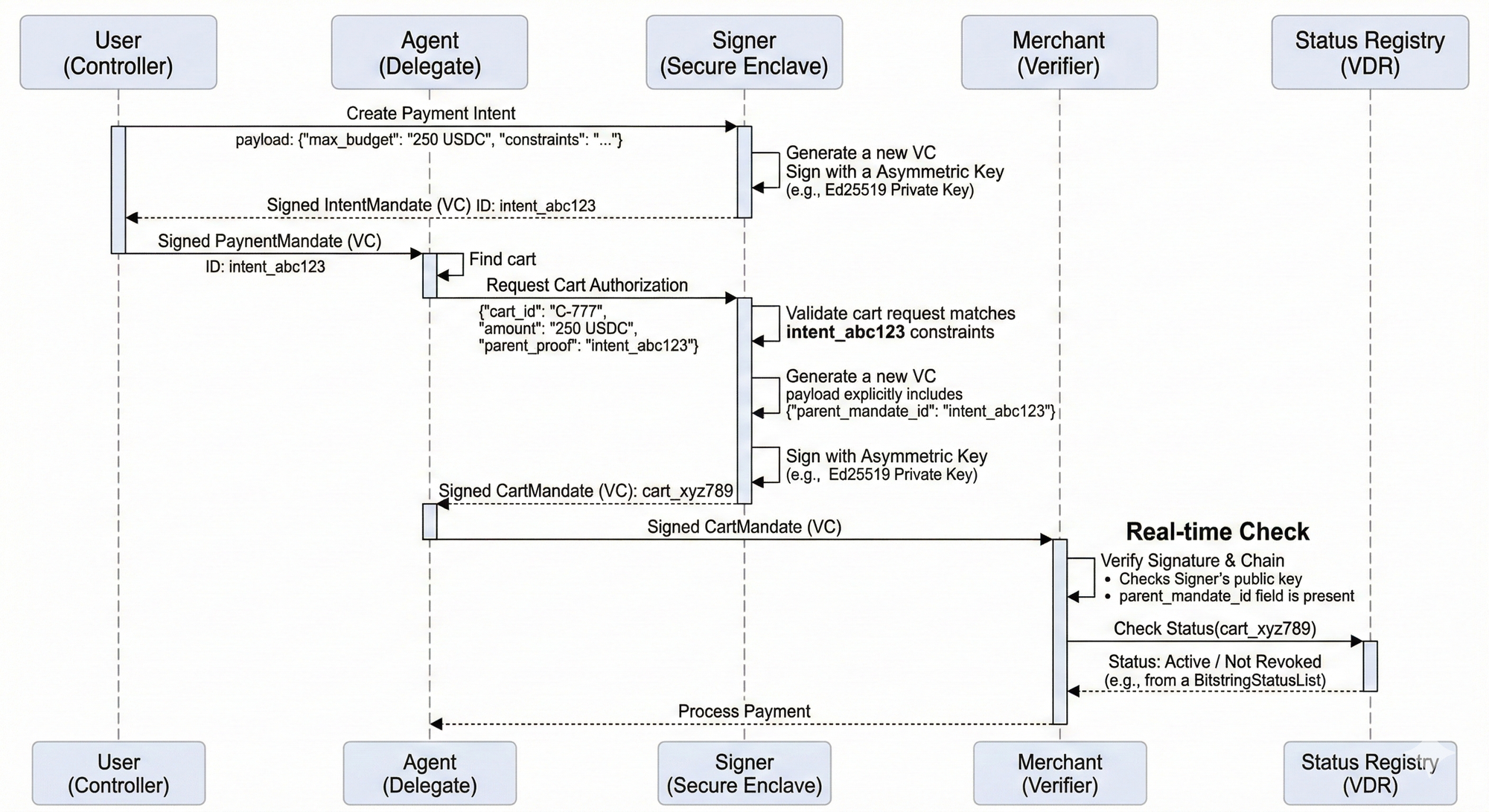
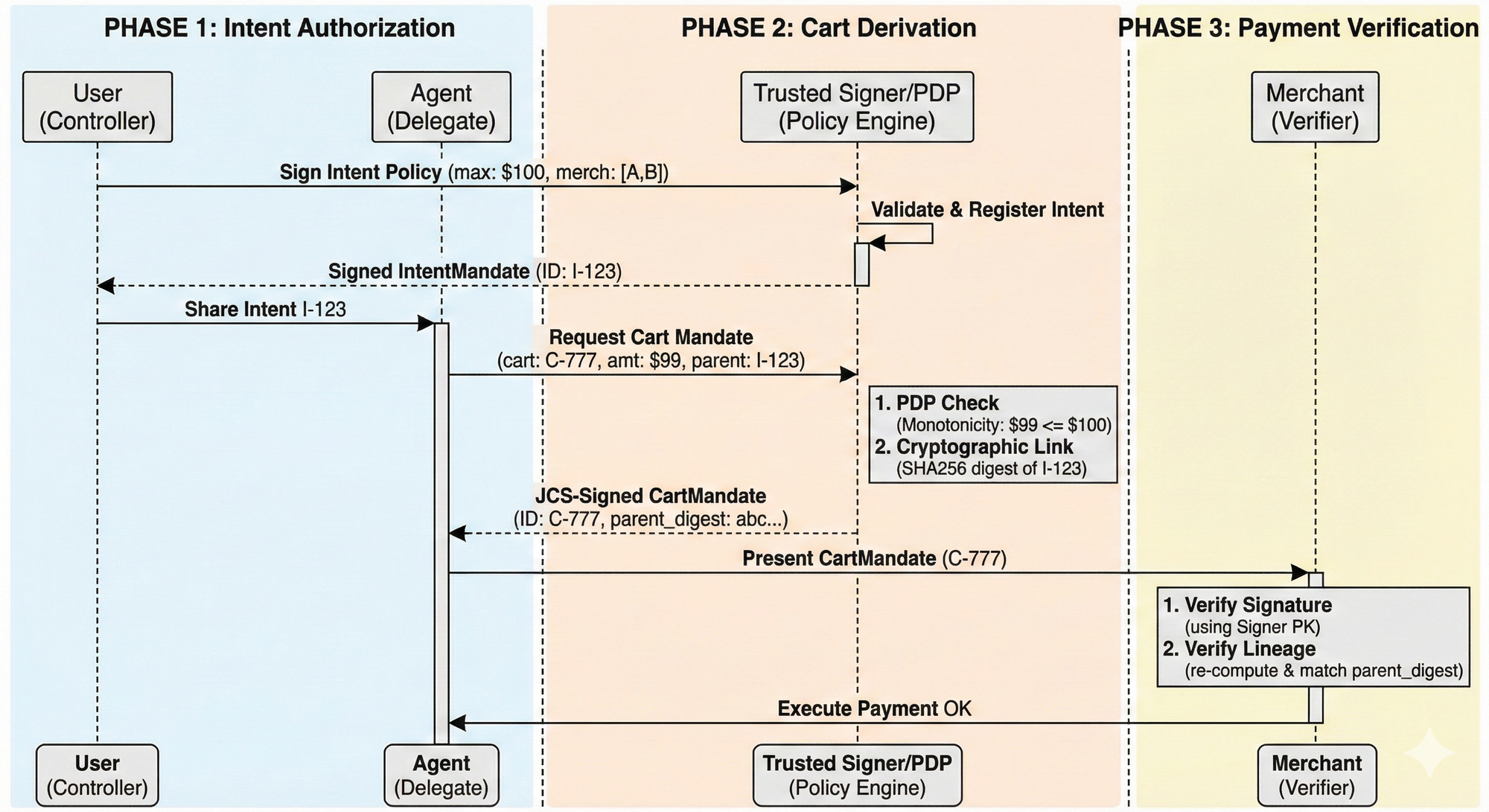
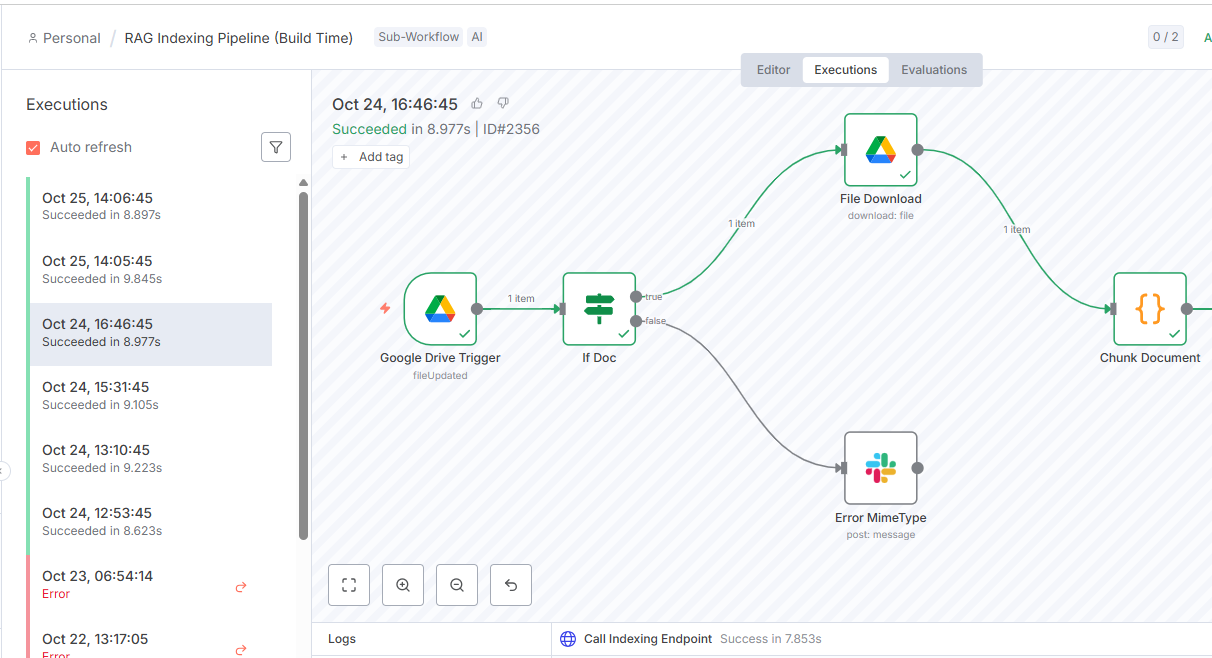
Inline code samples and modular mermaid diagrams will map three discrete phases. Phase One covers intent authorization. Phase two covers cart derivation. Phase three covers payment verification. Expect prescriptive, code first guidance aimed at security teams and senior technical leaders. Start here with urgency.
Root Cause & The Validation Chasm
Our audit found three decisive failure modes that let attackers fabricate mandates and persist valid-looking credentials. First, symmetric signing dominated implementations which lets verifiers forge authorizations. Second, cart-stage credentials frequently lacked a cryptographic link to their parent intent which enables fabricated-lineage attacks. Third, systems relied only on short expirations without a revocation registry which leaves a dangerous revocation window and creates operational friction and localized hurdles for incident response.
Symmetric Fallacy (HS256 liability)
Exploit scenario. An integrator used HS256 with a shared secret across services. An attacker who extracts that secret from a misconfigured CI (Continuous Integration) pipeline signs a fake CartMandate and presents it as user-authorized. Payment processors that accept HS256 treat the token as valid and process funds. Short sentence. Attackers reuse secrets across environments and scale fraud quickly.
// Forgery example using shared secret
from jose import jwt
secret = "leaked_demo_secret"
payload = {"mandate_id":"cart_999","user_id":"alice","final_amount":100}
token = jwt.encode(payload, secret, algorithm="HS256")
print(token) # any holder of secret can mint this token
Root cause. Developers chose symmetric JWT (JSON Web Token) for convenience and misconstrued non-repudiation properties; the protocol design left a migration path undefined which increased localized hurdles for secure key management and rotation.
The "Detached Signature" & Orphaned Mandate Risk
Exploit scenario. Agents submit CartMandates that are technically valid but cryptographically detached from their IntentMandate lineage. Malicious actors intercept a valid cart authorization and replay it against a different merchant or context. Verification endpoints fail because they validate the signature of the cart but skip the "Chain of Trust" check back to the user’s root key. The ledger records a valid transaction, but the stack trace is broken; effectively an "orphan" payment with no proven user intent.
// AP2 Vulnerability: The "Floating" Mandate
// The verifier checks the signature, but ignores the missing 'parent_mandate_id'
{
"type": ["VerifiableCredential", "CartMandate"],
"issuer": "did:key:z6MkhaXgB...",
"credentialSubject": {
"mandate_id": "urn:uuid:8938-...",
"cart_context": "cart_777",
"amount": { "value": 250, "currency": "USD" }
// CRITICAL MISSING LINK: "parent_mandate_id": "urn:uuid:intent_123"
},
"proof": { "type": "Ed25519Signature2020", "proofValue": "..." }
}The "Floating" Mandate
Root cause. Developers treated the parent_mandate_id as optional metadata rather than a cryptographic constraint. Service teams verified the Sender (the Agent) but failed to verify the Authority (the User), creating a "Confused Deputy" vulnerability where the agent is allowed to act outside the user's specific scope.
The "Status List" Latency Gap (Revocation)
Exploit scenario. A compromised agent key is revoked on the ledger, but payment gateways rely on cached credentialStatus lists. Attackers exploit this "propagation delay" (often 10-60 minutes) to double-spend or flush high-value transactions before the status bit flips. Teams relied on the credential's expirationDate (temporal trust) rather than performing real-time BitstringStatusList lookups (state verification).
# 2026 Vulnerability: Caching the Status List
# The verifier trusts a stale status list instead of fetching the latest proof
def verify_payment(presentation):
# Fails to check the live "StatusRegistry" smart contract or VDR
if presentation.expiration > now():
# VULNERABLE: Assuming valid if not expired
return process_tx(presentation)
# MISSING:
# status = resolver.resolve(presentation.status_list_index)
# if status.is_revoked(): raise RevokedCredentialErrorCaching the Status List
Root cause. The protocol emphasized off-chain efficiency (caching revocation lists to save gas/latency) but failed to mandate real-time checks for high-value thresholds. Developers misread "eventual consistency" as "immediate safety," leaving a predictable window for race-condition attacks.
Architectural Pivot: Asymmetry, Policy Engine, and Cryptographic Chain of Custody
Move signing from HS256 to ES256 immediately for non-repudiation and correct key semantics. ECDSA (Elliptic Curve Digital Signature Algorithm) using P-256 separates signing authority from verification duties; private keys remain with wallet operators and public keys circulate via a trusted key-distribution channel. This change prevents any verifier from impersonating a signer and reduces blast radius when a verifier platform suffers a breach.
Asymmetric Pivot. ECDSA yields three concrete gains. First, non-repudiation. Only the private key holder can produce a valid signature; verifiers cannot forge evidence. Second, scalable key distribution. You publish a public key set with versioned identifiers and rotate without sharing secrets. Third, compact KID (Key Identifier) usage. Embed a key identifier in the JWT header to look up the proper public key quickly; the verifier checks KID then validates the ECDSA signature.
Signer.py as a Dumb Pure Primitive. Keep signing code single purpose. The signer must canonicalize payloads deterministically, compute a byte-level digest, and return a compact signature token. The signer must not interpret business constraints, mutate domain objects, validate policy, or fetch parent mandates. Keep it small and testable; simpler primitives reduce bug surface and keep business logic above the crypto layer.
Signer Minimal Interface
The Signer class provides a pure primitive for cryptographic operations using JSON Canonicalization Scheme (JCS). Unlike legacy JWTs which sign Base64 blobs, this signer handles raw JSON objects, requiring strict canonicalization (RFC 8785) to ensure the byte-stream is identical across Python, Go, and JS environments.
# Signer: Pure Primitive (JCS Implementation)
# Dependency: strict_rfc8785_canonicalizer
import hashlib
from ecdsa import SigningKey, NIST256p
class Signer:
def __init__(self, private_key_pem: str, kid: str):
self.sk = SigningKey.from_pem(private_key_pem)
self.kid = kid
def _canonical_bytes(self, payload: dict) -> bytes:
# RFC 8785: Deterministic JSON (sorted keys, no whitespace)
return jcs.serialize(payload).encode('utf-8')
def sign(self, payload: dict) -> dict:
# Returns a JWS Compact Serialization or a generic Proof Object
secured_input = self._canonical_bytes(payload)
# Sign the SHA256 digest of the canonical bytes
sig = self.sk.sign(secured_input, hashfunc=hashlib.sha256)
return {
"payload": payload,
"signature": base64url_encode(sig),
"kid": self.kid,
"alg": "ES256"
}Pure Primitive (JCS Implementation)
Canonicalization Rules (The "what you see is what you sign" standard)
Serialize JSON with stable lexicographical key ordering (lexical order or dictionary order keys). Escape characters must follow RFC 8785. Normalize numbers (e.g., 250 not 250.00). Hash the UTF-8 bytes of this stable structure. This prevents "Semantic Wrapping" attacks where the JSON parser sees one value (due to duplicate keys) but the signature validator sees another.
Signature Payload Structure
Sign the canonicalized mandate body, excluding the signature field itself to prevent recursion. The payload must include a metadata block containing mandate_type, subject_id, issued_at, expires_at, and—for child mandates—an intent_digest.
- Verification Logic: Unlike legacy JWTs which verify opaque Base64 strings, the AP2 verifier must first canonicalize the received JSON payload (RFC 8785) to recreate the deterministic byte sequence, and then validate the signature against those bytes. This ensures the "logic" seen by the policy engine matches the "bytes" verified by the crypto engine.
// Header indicating JCS (JSON Canonicalization) usage
{
"alg": "ES256",
"kid": "user-wallet-v1",
"b64": false, // Critical: Indicates payload is detached/unencoded JSON
"crit": ["b64"]
}Signature Mandate Payload Header Indicating JCS (JSON Canonicalization) Usage
Mandate Policy Engine (PDP & PEP)
Split responsibilities clearly. The Policy Decision Point (PDP) evaluates logic (monotonicity, constraints), while the Policy Enforcement Point (PEP) gates the execution. This ensures the Signer (PEP) never signs a payload that hasn't been "green-lit" by the PDP.
- Parent-chain verification: Validate that
parent_mandate_idexists and its signature is valid. - Monotonicity: Ensure the child mandate is a strict subset of the parent's permissions.
- PEP Separation: The Signer is "dumb"—it does not fetch data or validate rules. It only signs what the PDP approves.
Failure Responses
Do not return generic HTTP 400 errors. Agents require explicit, machine-parsable error enums to determine their next action (e.g., retry with a lower amount vs. abandon cart).
- Standardized Enums: Return precise codes like
INVALID_SIGNATURE(crypto failure),EXPIRED_INTENT(temporal failure),BOUNDS_VIOLATION(policy failure: over budget), orMERCHANT_MISMATCH(policy failure: wrong vendor). - Audit Emission: Every failure must emit a structured audit log containing the timestamp, the kid used for verification, the problematic mandate IDs, and the specific policy rule that triggered the denial. This is essential for post-hoc dispute resolution when a user asks, "Why didn't my agent buy this?"
Hierarchical Hash-Binding (The "Chain of Trust")
To solve the "Orphaned Credential" problem, every CartMandate must explicitly embed the Cryptographic Digest of its parent IntentMandate. This binds the payment to the specific user intent, making "Replay Attacks" impossible.
# Embedding Intent Digest inside CartMandate
# This creates a "Merkle-like" chain of custody
cart_payload = {
"type": "CartMandate",
"cart_id": "c_777",
"amount": {"val": "42.50", "cur": "USD"},
# BINDING FIELD:
"parent_digest": sha256(jcs.serialize(intent_mandate)).hexdigest(),
"parent_kid": intent_mandate['kid']
}
# The signature now covers the cart AND the link to the parent
signed_cart = signer.sign(cart_payload)Embedding Intent Digest inside CartMandate
Monotonicity of Bounds (The Decorator)
The PDP enforces that an agent cannot expand its own budget. We define this formally: Child.Amount <= Parent.Amount and Child.Scope ⊆ Parent.Scope.
# Policy Engine Decorator: Enforcing Monotonicity
from decimal import Decimal
class PolicyViolation(Exception): pass
def enforce_monotonicity(func):
def wrapper(child_payload, parent_payload):
# 1. Currency Lock
if child_payload['amount']['cur'] != parent_payload['budget']['cur']:
raise PolicyViolation("CURRENCY_MISMATCH")
# 2. Budget Squeeze (Child <= Parent)
child_val = Decimal(child_payload['amount']['val'])
parent_val = Decimal(parent_payload['budget']['val'])
if child_val > parent_val:
raise PolicyViolation(f"OVERSPEND: {child_val} > {parent_val}")
# 3. Merchant Whitelist (Child ⊆ Parent)
allowed = set(parent_payload.get('merchants', []))
target = child_payload.get('merchant_id')
if allowed and target not in allowed:
raise PolicyViolation(f"UNAUTHORIZED_MERCHANT: {target}")
return func(child_payload, parent_payload)
return wrapperEnforcing Monotonicity in AP2
Developer ergonomics
Ship a strict SDK. Do not ask developers to "implement canonicalization"—they will fail. Provide sdk.sign(dict) and sdk.verify(dict) that handle the JCS normalization internally. Include KeyLookup utilities that fail fast if a KID is missing, preventing vague "Signature Invalid" errors.
Ship strict types for Money and MerchantId and include clear error enums. Unit tests should include canonicalization cross-language checks so Java, Go, and Python produce identical digests. Provide a key lookup that reads KID (Key Identifier) and fails fast if absent; surface human-friendly messages for integrators.
This architecture prevents the Validation Chasm from migrating into the crypto layer by enforcing a strict separation. Keep signer.py pure and deterministic; push policy, lineage checks, and monotonic constraints into the PDP. That way verification checks fail loudly with clear codes and the cryptographic primitive remains small, testable, and auditable.
Operational Playbook: Key Management & Lifecycle
Key Storage & Access
- User Keys (The Edge): Store private keys in hardware-backed user wallets (Secure Enclave / Keystore). Users never export raw key material; they only sign intent payloads.
- Service Keys (The Cloud): Host operator/signer private keys in KMS HSMs (e.g., Cloud KMS, Vault) with strict RBAC. Use Attestation constraints to ensure keys can only be used by the
Signerprimitive we defined earlier.
Distribution (DID vs. JWKS)
Instead of raw JWKS endpoints, publish DID Documents (Decentralized Identifiers).
- Why: A DID Document (e.g.,
did:web:example.com) wraps your keys (JWK Set) with Verification Methods. This allows you to rotate keys without breaking the user's trust anchor, as they trust the DID, not just the specific key currently in use. - Discovery: Serve the DID document with strict
Cache-Controlheaders to balance propagation speed with caching efficiency.
Revocation Strategy (Status Lists vs. CRLs)
Abandon legacy CRLs (Certificate Revocation Lists) which are bandwidth-heavy. Adopt Bitstring Status Lists (common in VC standards).
- Mechanism: A "Status List" is a compressed bit-array (e.g.,
0010...) where each index corresponds to a mandate. To revoke mandate #3, you simply flip bit #3 to1. - Performance: Verifiers fetch this tiny bitstring (cached via CDN) and check the index locally. This offers O(1) lookups with zero false positives, unlike Bloom filters.
- Incident Response: In a breach, update the Status List immediately. Verifiers using "Real-Time Check" (Phase 3) will reject the compromised mandate instantly.
Audits & SLAs
- Immutable Logging: The Policy Engine (PDP) must log the canonicalized input hash and the policy decision to an append-only ledger (or Write-Once-Read-Many storage).
- Latency Budget: The "Payment Verification" phase (Phase 3) must complete under 100ms. This requires caching the DID Document and Status List at the edge, so the only real-time call is the cryptographic signature verification.
Final Reflection: The Business of Trust
Solving AI agent payment authentication is not just a technical checkbox; it is the fundamental enabler of the Agent Economy.
By moving from "Shared Secrets" (Symmetric Fallacy) to Cryptographic Lineage, we transform a high-risk operational burden into a competitive asset.
- For Engineering: It creates a "Validation Chasm" that isolates sensitive crypto code from messy business logic, reducing the "blast radius" of bugs and making audits trivial.
- For Product: It enables Non-Repudiation. When an agent spends money, the cryptographic chain proves exactly which user intent authorized it. This eliminates vague chargebacks and builds the trust required to raise transaction limits.
- For the Business: It turns compliance (AP2) into speed. A robust "Policy Engine" allows you to safely onboard new merchants and launch new agent capabilities without waiting for security reviews on every minor change.
Prioritize simple primitives (dumb signers), explicit policy (smart engines), and real-time revocation (status lists). When done well, this architecture turns "Agent Payments" from a scary liability into a trusted, high-growth revenue channel.
Methodology & Transparency
This 2587-word technical analysis was recursively architected using a multi-agent orchestration framework. Concepts were synthesized through a combination of contextual grounding and forensic technical auditing to ensure architectural accuracy.



Comments
Sign in to join the conversation
Sign In